Azure AD Conditional Access
Last week Microsoft made Azure AD conditional Access publicly available. Let me explain what it is and why we would like to have this.
What is it?
First let’s talk about what it is. Azure AD conditional access lets you decide per application in Azure AD how your authentication should be handled. By default all the applications use the same kind of authentication. It does not matter if you are inside the company walls or at Starbucks.
Why would we want it?
As most of you know is that inside the company walls we have all kind of extra security before you can access the application that you need. At entering the company, we need to use our entry card to access the building before we can access the network. When we are using Azure AD for accessing our applications we do not need to be on the company’s network and can access the application from every internet point.
Azure AD has the ability to have multifactor authentication (MFA), but that always was on or off for everything wherever you are. So you got challenged with MFA also when you were inside the office. For almost all the users this gets annoying and will stop using the application if possible or complain that they cannot work that way and that is understandable. We already had the ability to set IP addresses with MFA authentication. That is usable for 1 company with a few external IP addresses, but not when you have multiple office with local internet breakouts. The limit in Azure MFA is a maximum of 20 IP’s.
With Azure AD conditional access, we still have the option to enable MFA for everything and use the IP’s to check if you are inside the office to skip MFA. With conditional access we can select different settings for different applications, google analytics does not have the same requirements as your CRM system
How to configure
The configuration is fairly simple; we must use the old Azure portal https://manage.windowsazure.com and select the AD.
This feature is only available when you have Azure AD Premium.
When you are in the AD go to applications and select the application you want to configure and select the configuration tab. This tab can be different depending on the application. 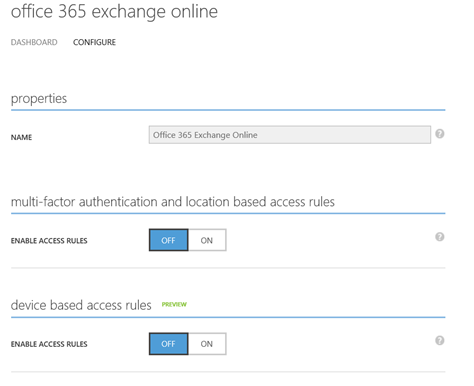
These are the settings for Exchange Online. Here you can set the authentication based on the location (IP based) or on the compliance of your device. The last one is in preview now but a very powerful one. You can also create these settings to apply only for a set of users. I did not see a scenario where this could be a requirement.
Conclusion
I find this a great addition to the configuration options and usability of Azure AD and keeping your data secure where possible. Most users want their data save, but do not want that at the cost of usability. The usually understand that when they are outside the office extra security is necessary.